Complemento
Collection of tools.
|
:[ Menu ]: |
|
: [ Current Version 0.7.7 - 2011 ] : |
Acri Emanuele <crossbower@gmail.com>
NEWS: Complemento officially included in BackTrack Linux 5

Complemento is a
collection of tools I originally grokked up for my personal
toolchain, to solve some network problems or just for fun.
I have released it to the public a couple of years ago, but the tools continue to be developed and refined.
- LetDown is a tcp flooder I have programmed
after reading Fyodor article "TCP Resource Exhaustion and Botched
Disclosure" (you can read it at http://insecure.org/stf/tcp-dos-attack-explained.html).
It uses an experimental userland TCP/IP stack, and supports multistage payloads for complex protocols, fragmentation of packets and variable tcp window. It's not a simple syn flooder, but a powerful tool able to interrupt the communication at any stage of the TCP protocol.
Note: LetDown is based on Fyodor NDos, it's not about vulnerabilities disclosed by Outpost24 team.
Update: The link to the article is no longer available but you can read http://old.nabble.com/TCP-Resource-Exhaustion-Attacks-td19777386.html instead...
- ReverseRaider is a domain scanner that uses various techniques,
such as wordlist scanning to find target's subdomains or
reverse resolution for a range of ip (thanks to Jeremy Brown and his
tool DomainScanner for the idea. His blog is: http://jbrownsec.blogspot.com/).
It's fully multi-threaded and supports permutation on wordlist, IPv6 and various DNS options (e.g. no-recursion).
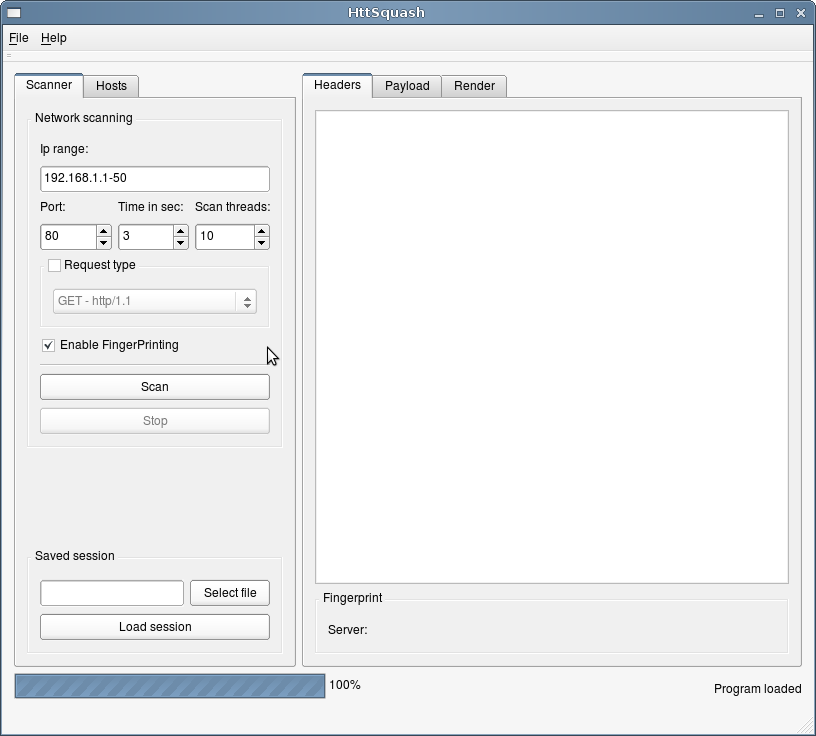
- Httsquash
is an http server scanner, banner grabber and data retriever (there's a GUI interface for it). It can be used to scan large
IP ranges to find networked devices or http servers.
It supports IPv6, various HTTP request methods and an experimental fingerprinting system, based on httprecon signatures (http://www.computec.ch/projekte/httprecon/).
Compilation and dependencies
Required libraries:
LetDown:
libpcap (http://www.tcpdump.org/).
python-dev (http://www.python.org/).
ReverseRaider:
c-ares (http://c-ares.haxx.se/).
HttSquash:
posix threads (pthread).
libcurl (http://curl.haxx.se/libcurl/).
LetDown Video
The effects of a LetDown DoS attack.
The video may take some seconds to download. I also noticed that sometimes reloading the page can help...
Loading the player ...
LetDown
Usage:
LetDown 3wh+payload flooder v0.7.7 - Acri Emanuele (crossbower@gmail.com)
Usage:
letdown -d dst_ip -p dst_port -D dst_mac [options]
Options:
-d destination ip address, target
-D destination mac address or router mac address
-p destination port
-s source ip address
-S source mac address
-x first source port (default 1025)
-y last source port (default 65534)
-l enables infinite loop mode
-i network interface
-t sleep time in microseconds (default 10000)
-a max time in second for waiting responses (default 40)
Extra options:
-v verbosity level (0=quiet, 1=normal, 2=verbose)
-f automagically set firewall rules for blocking
rst packet generated by the kernel
examples: -f iptables, -f blackhole (for freebsd)
-L special interaction levels with the target
s syn flooding, no 3-way-handshake
a send acknowledgment packets (polite mode)
f send finalize packets (include polite mode)
r send reset packets (check firewall rules...)
-W window size for ack packets (ex: 0-window attack)
-O enable ack fragmentation and set fragment offset delta
-C fragment counter if fragmentation is enabled (default 1)
-P payload file (see payloads directory...)
-M multistage payload file (see payloads directory...)
ReverseRaider
Usage:
ReverseRaider domain scanner v0.7.7 - Acri Emanuele (crossbower@gmail.com)
Usage:
reverseraider -d domain | -r range [options]
Options:
-r range of ipv4 or ipv6 addresses, for reverse scanning
examples: 208.67.1.1-254 or 2001:0DB8::1428:57ab-6344
-f file containing lists of ip addresses, for reverse scanning
-d domain, for wordlist scanning (example google.com)
-w wordlist file (see wordlists directory...)
Extra options:
-t requests timeout in seconds
-P enable numeric permutation on wordlist (default off)
-D nameserver to use (default: resolv.conf)
-T use TCP queries instead of UDP queries
-R don't set the recursion bit on queries
HttSquash
Usage:
HTTSquash scanner v0.7.7 - Acri Emanuele (crossbower@gmail.com)
Usage:
httsquash -r range [options]
Options:
-r range of ip addresses or target dns name
examples: 208.67.1.1-254, 2001::1428:57ab-6344, google.com
-p port (default 80)
Extra options:
-t time in seconds (default 3)
-m max scan processes (default 10)
-b print body of response (html data)
-S use HTTPS instead of HTTP
-T custom request type (default GET)
-U custom request URL (default /)
-H set an header for the request (can be used multiple times)
examples: Keep-Alive:300, User-Agent:httsquash
Script options:
-j cookie jar separator ("%%")